Picture a standard Monday morning in a mid-sized logistics firm in Pune. An employee unknowingly clicks a sophisticated phishing link. In a traditional setup, that single click might grant an attacker access to the kernel, allowing them to bypass software-based antivirus and exfiltrate sensitive customer data. But in an organization with a correct device strategy, the story ends differently. The device’s hardware-level security—a discrete “security chip”—detects the unauthorized attempt to modify system files and shuts it down before the operating system even realizes it’s under attack. In 2026, relying solely on software to protect your business is like putting a high-tech lock on a cardboard door. As cyber-physical threats converge and India’s regulatory landscape tightens, the importance of “secure-by-design” hardware has moved from the server room to the boardroom.
For years, the prevailing belief in IT was that security was a software problem. You bought the best hardware your budget allowed, and then “bolted on” security layers: a firewall here, an antivirus there, and a VPN for remote work. This “layered” approach worked when threats were primarily external and software-based.
What we’re seeing now is the rise of firmware and boot-level attacks that software simply cannot see. If the foundation—the hardware itself—is compromised, every software-based security measure sitting on top of it becomes a house of cards. Standard laptops without specialized security processors are increasingly vulnerable to “Adversary-in-the-Middle” attacks that occur during the boot process. You can’t patch a hardware flaw with a software update. By treating hardware as a commodity and security as an afterthought, businesses are leaving a massive back door open for sophisticated actors.
The numbers reveal a stark reality for the modern enterprise. These aren’t just technical glitches; they are existential threats.
Furthermore, the data shows that the financial impact of a breach is significantly higher for organizations lacking hardware-rooted security. In 2026, “effective protection” is measured by the speed of hardware-level detection. Hardware-based security modules (HSMs) and Trusted Platform Modules (TPMs) are now the baseline for any business that processes more than just public information.
Rarely do the best leaders wait for a breach to happen before auditing their fleet. Instead, they are adopting a “Zero Trust” posture that starts at the silicon level. They ensure every device in their ecosystem has a “Hardware Root of Trust”—a unique, immutable identity baked into the chip that verifies the integrity of the system every time it starts up.
These leaders are also moving toward “Confidential Computing.” This technology protects data not just “at rest” (on the drive) or “in transit” (over the web), but also “in use.” By creating hardware-isolated enclaves in the CPU, businesses can process sensitive data even in potentially compromised environments. For an Indian SME or a large GCC, this means you can run complex analytics on sensitive customer data without it ever being visible to the underlying operating system or unauthorized administrators.
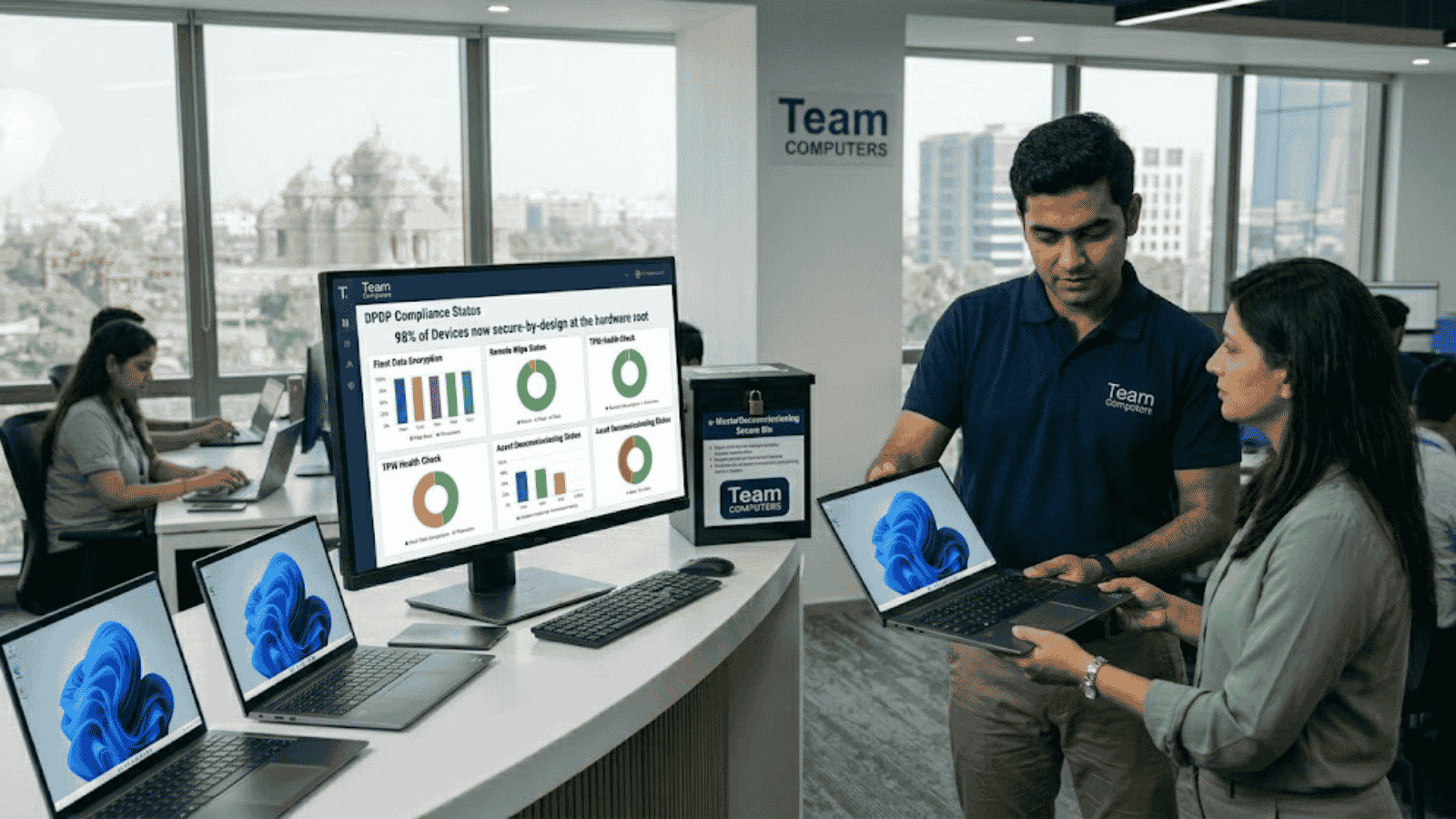
Here’s where the pressure gets real: the Digital Personal Data Protection (DPDP) Act 2023 is now in full swing. For any Indian business, a data breach isn’t just a technical failure; it’s a potential legal catastrophe with penalties reaching up to ₹250 crore. The Act mandates “reasonable security safeguards,” and in 2026, hardware-level encryption and secure boot are no longer “extras”—they are the definition of reasonable.
The Indian market is also unique due to the sheer volume of “mobile-first” workers. Whether it’s a field agent in rural Uttar Pradesh or a consultant in a Delhi cafe, your data is constantly on the move. Secure-by-design devices ensure that even if a laptop is physically stolen, the data remains a brick to the thief. In a country where the “device-to-employee” ratio is exploding, the hardware is your last, most reliable line of defense against both physical and digital theft.
Many small business owners believe they are “too small to be a target.” But “good enough” security makes you the perfect “stepping stone” target. Attackers often use smaller, less secure partners to gain entry into the supply chains of larger enterprises. If your device doesn’t secure data from the start, you aren’t just a risk to yourself; you’re a liability to your entire ecosystem.
Moreover, the transition to AI-driven operations requires hardware that can keep up. Modern AI PCs come with integrated NPUs (Neural Processing Units) that don’t just speed up tasks—they can run local AI-based security agents that monitor for anomalous behavior in real-time without sending data to the cloud. This keeps your proprietary business logic and sensitive data exactly where it belongs: on the device.
The biggest mistake we see is companies buying “consumer-grade” hardware for “enterprise-grade” problems. A consumer laptop might have the same processor as a business model, but it often lacks the dedicated security chips (like vPro or Ryzen Pro) that manage out-of-band updates and hardware-level isolation. You might save ₹5,000 upfront, but you’re effectively subsidizing the future cost of a breach.
What we’ve learned over 38 years at Team Computers is that security is only as strong as its weakest link—and for many, that link is a three-year-old laptop with an unpatched BIOS. Most Indian firms are sitting on a “technical debt” of insecure hardware. By modernizing your fleet with secure-by-design devices, you don’t just improve performance; you automate your compliance.
Moving forward, the focus must shift to IT asset lifecycle management that includes secure decommissioning. A secure device strategy isn’t just about how you start; it’s about ensuring that when a device reaches its end-of-life, the data it held is permanently and irrecoverably destroyed at the hardware level.
The path to a resilient business doesn’t require you to be a cybersecurity expert—it requires you to choose hardware that was built by experts. If you don’t know if your current fleet supports hardware-level encryption or has a “self-healing” BIOS, you’re flying blind in a storm that’s only getting stronger.
Your devices are the frontline of your digital fortress. If the frontline is weak, your entire organization is exposed. It’s time to stop treating hardware security as an optional feature and start treating it as the foundation of your business continuity.
Not sure if your current devices meet the new DPDP security standards? Our experts will conduct a thorough audit of your hardware fleet to identify vulnerabilities and recommend a “secure-by-design” roadmap tailored to your business size and budget.