With the increasing changes and challenges in the market, it is extremely important to keep up with the pace of modernization. Fortunately enough, G Suite aims to drive transformations across organizations, promote cultures of collaboration and empower employees to rethink the way they work. All this, with the main aim to cultivate, enhance and promote productivity in the organization’s functioning!
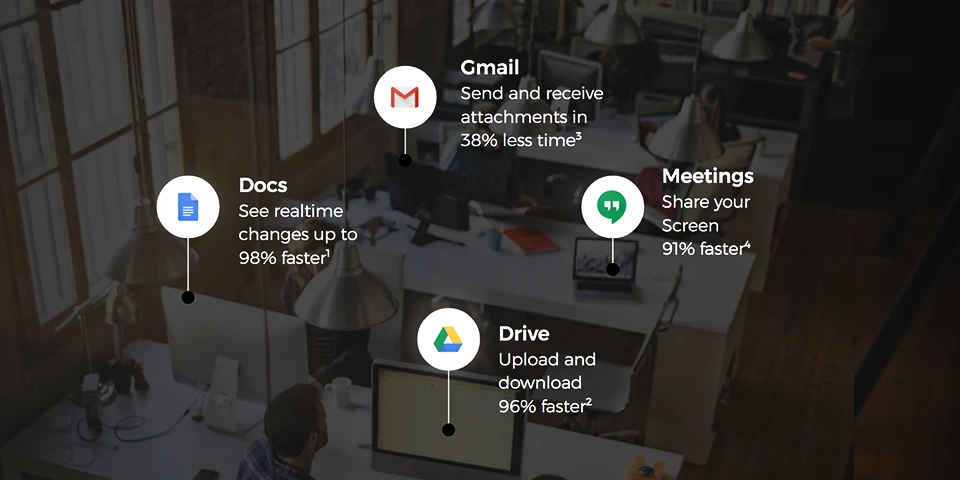
The efficiency gains that are envisioned with G Suite’s robust set of collaboration tools and features are as follows:-
- Easy and effective employee collaboration with real-time editing in Google Docs, Slides, Sheets and other tools.
- Provision of feedback from anywhere, irrespective of the device!
- Reduction in the number and length of meetings and discussions with Google Meet and Hangouts.
- Security and software updates being processed automatically to discourage lengthy and inconvenient disruptions to keep devices and hardware up to date.
The familiarity and acceptability of G Suite in users’ personal lives, coupled with the intuitive design of the tools, leads to a significant decrease in on-demand IT and help desk tickets, freeing up additional time for IT to focus on value-adding initiatives. G Suite built-in security features such as advanced anti-phishing, security center, mobile management, etc give admins simpler and more streamlined ways to manage users. All of these features are included with G suite at no additional cost because it is at its heart to control devices, ensure compliance and keep data secure. G suite, is thus, built from the ground up around security. That’s the biggest selling point of Google! Check out the following reasons to boost your system’s productivity with G Suite:-
- Artificial Intelligence and Machine learning
G Suite’s AI and Machine Learning are integrated throughout and operate like a personal assistant. So, schedule meetings in Calendar, acquire suggestive responses based on Gmail content and even track down relevant web documents relating to the undertaken projects in Sheets, Docs, and Slides.
2. Drive and Vault
Don’t drown in your own research searching for information! Put to use G Suite features Drive and Vault, the two repository tools to always have access to the most recent version of every file! No more searching through endless email threads or even having to send file attachments! What’s the difference between Vault and Drive, you ask? Files in Drive can further be edited, while Vault is used to store completed documents.
 3. Break the geographical barriers
3. Break the geographical barriers
Business travel is solely expected to cost trillions by 2020! Invest in live, real-time discussions, and avoid travel costs and time! Use Google Hangouts to share and discuss files, even record them for future references! Sync Hangouts with Google Calendar for increased efficiency and collective invites. Gmail, Hangouts, and Calendar are all connected, so if you were to set up a meeting in Calendar, it can easily be assigned to other users for Hangouts and notified via Gmail.

4. Planning and organizing, now a cakewalk!
Google Forms is an excellent survey tool that organizations can use to plan events, organize their priorities and collect data through questionnaires. You can also share a link to a form via social media channels or email and track answers in Google sheets.
5. Bring teams together
Create Team Drives with G Suite to limit the sharing of links to documents that need to be accessed by a group of employees. Everyone on the team would have access to these files through a shared space for cloud storage. Back and forth communications across time zones are extremely convenient with the presence of the previous version of documents in files. Bottom line? G Suite helps your business run optimally- and that spells more revenue.
 6. Zero maintenance stress
6. Zero maintenance stress
G Suite doesn’t need any maintenance and is designed to keep everything updated. There’s no need to worry about hardware or software maintenance related issues. Save money, save time and save your data, without reminding yourself to “save”.
7. Marketplace
Can’t find what you’re looking for? Not a problem- just hop on over to the G Suite Marketplace to browse countless third-party apps and tools. With the marketplace, you can customize and revamp your digital workplace. With a G Suite plan, businesses enjoy 30GB of storage space, unlimited Google Group email addresses, 24/7 phone and email support, and compatible add-ons available through the G Suite Marketplace.

8. Say no to ADs
Unlike other free consumer software, though, free G Suite users don’t see ads while using the services. Google also doesn’t use the information stored in G Suite applications and accounts for advertisement purposes.
9. Create your own websites!
Google Sites was added in 2008 as the G Suite website builder. It allows users to create websites with little to no coding knowledge or design skills. Landing pages and project websites can be created using pre-made templates to be published internally or publicly.
10. Proactive hijacking protection
Google provides an automatic, proactive layer of security to protect all users against account hijacking. It asks for proof to confirm your identity to provide access. An SMS code is sent to a recovery phone number which helps block automated bots, bulk phishing, and targeted attacks.

Having a consistent, seamless, collaborative experience across devices allows employees to continue to be actively engaged in projects even when they were traveling or working remotely. Added to this, were the intelligent features in the calendar, like finding the time or automatic room booker, which makes the meetings easier to schedule and removes frictions to join. Increase in productivity is the prime agenda for Google that promotes access to relevant information, easily and effectively. At the organizational front, it significantly reduces the time and resources required to manage legacy infrastructure including activities related to creating and provisioning accounts and managing access.
Undoubtedly, G Suite is an all loaded platform to deal with all business needs and expectations without having to deal with the worries of costs and revenues!
G Suite comes with an annual subscription cost per user, with an SSO solution included in the G Suite license. So why wait? Switch to Google to enable an unparalleled working experience!
(Please note: Google offers a period of a free trial, so that there are no issues before committing to anything)











 3. Break the geographical barriers
3. Break the geographical barriers
 6. Zero maintenance stress
6. Zero maintenance stress 

![SAP HANA on Cloud [3 considerations before hosting]](https://teamcomputers.com/wp-content/uploads/2019/05/sap-hana.webp)



