In today’s fast-paced business world, data is the new currency. Companies are increasingly relying on data to make informed decisions. This is where business analytics comes into play.
Business analytics involves analyzing data to gain insights and drive strategic decisions. It helps businesses understand trends, patterns, and anomalies. This understanding leads to better decision-making and improved performance.
The demand for business analytics solutions and services is growing rapidly. Organizations are seeking ways to harness data for competitive advantage. They need tools and expertise to transform raw data into actionable insights.
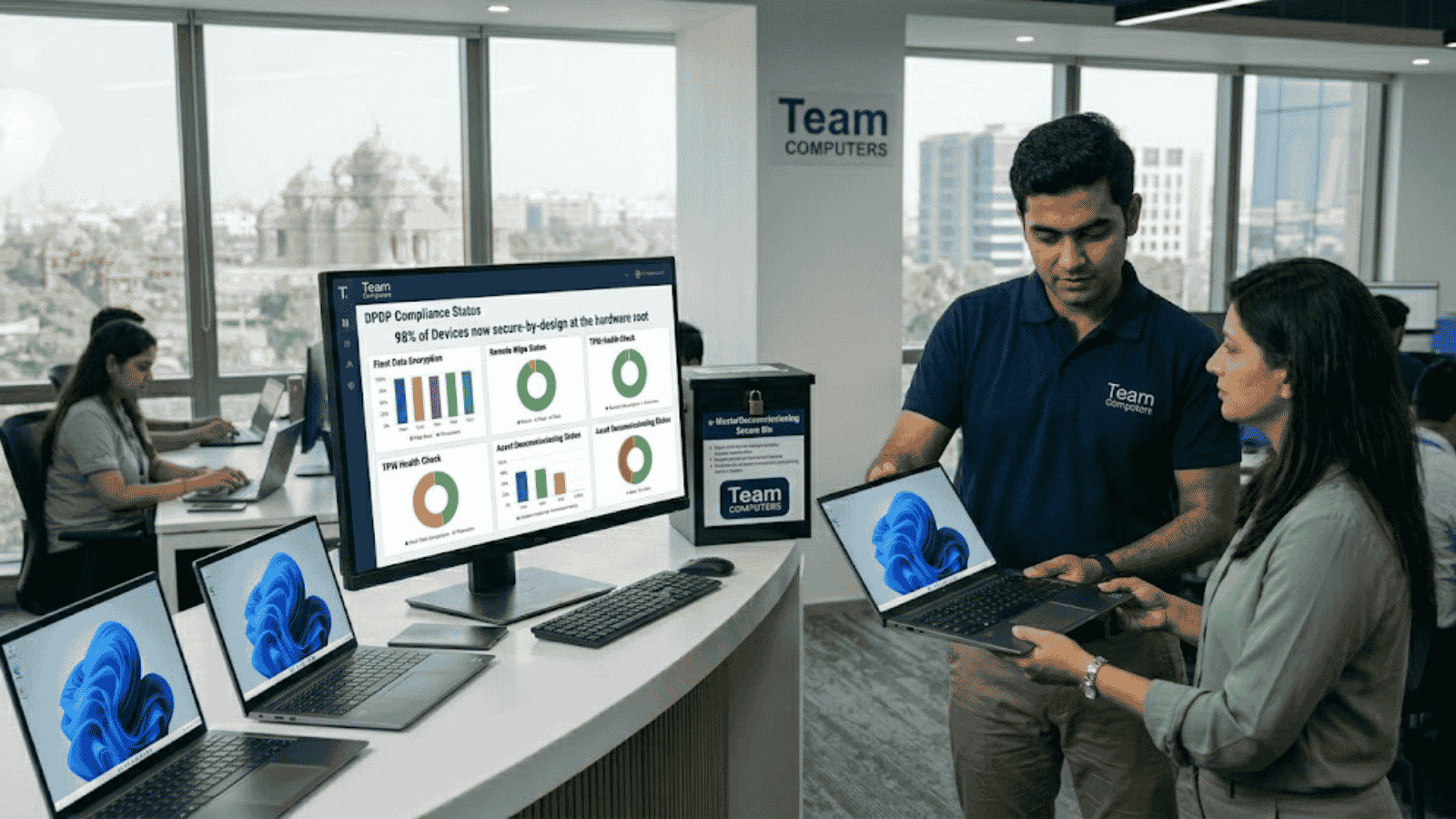
By leveraging these technologies, Team Computers helps businesses optimize operations and enhance efficiency. Their approach is rooted in innovation, integrity, and sustainable growth. This commitment ensures long-term success for their clients.
What is Business Analytics?
Business analytics is a methodical exploration of data. It focuses on statistical analysis and comes in different forms. The goal is to transform data into insights that drive business growth.
At its core, business analytics involves the use of quantitative methods. These methods include predictive modeling and statistical algorithms. They help predict future trends and behaviors.
There are several components integral to business analytics. These include data mining, data aggregation, and data modeling. Each plays a crucial role in deriving meaningful insights from raw data.
Business analytics serves various purposes within an organization:
- Identifying Opportunities: Discover untapped markets and new product opportunities.
- Enhancing Efficiency: Optimize processes to reduce costs and improve productivity.
- Improving Customer Experience: Use data to tailor products and services to customer needs.
With the rise of big data, the scope of business analytics has expanded. Now, it encompasses not only structured data but also unstructured data. This data comes from social media, sensors, and other diverse sources.
The impact of business analytics is immense. It equips organizations with the tools needed to navigate complex markets. The insights generated are used to align strategies with business goals.
By implementing business analytics, enterprises can shift from reactive to proactive strategies. They benefit from foresight instead of hindsight. This strategic edge is crucial for staying competitive in dynamic environments. The ability to predict and adapt can define success in today’s market.
The Four Pillars of Business Analytics: Descriptive, Diagnostic, Predictive, and Prescriptive
Understanding data begins with the right framework. Business analytics revolves around four main pillars. These are descriptive, diagnostic, predictive, and prescriptive analytics.
Descriptive Analytics provides a straightforward look at data. It answers the question, “What happened?” through summarizing past performance. This pillar uses key performance indicators (KPIs), dashboards, and reports.
Diagnostic Analytics digs deeper into data. It explores “Why did it happen?” by identifying patterns and correlations. Techniques include drill-down, data discovery, and correlations.
- Useful Techniques: Data correlation, data discovery
- Goal: Understand causes behind outcomes
Predictive Analytics leaps into the future. It asks, “What could happen?” by forecasting potential outcomes. By leveraging statistical models, this pillar anticipates trends and customer behaviors. Data mining and machine learning are central to this type of analytics.
- Key Methods: Machine learning, forecasting models
- Objective: Anticipate future trends
Prescriptive Analytics shifts focus to advice. It answers, “What should we do about it?” by recommending actions. This pillar uses optimization and simulation models. It guides decision-making by suggesting pathways to achieve desired outcomes.
- Primary Tools: Optimization algorithms, simulation
- Aim: Recommend strategic actions
These pillars work in harmony, providing a comprehensive view of data. Together, they empower companies to refine their strategies. Each pillar builds on the last, forming a robust analytic continuum.
The progression from descriptive to prescriptive highlights complexity. As data moves through these stages, the insights become more actionable. Organizations utilize these insights to make informed decisions, moving beyond guesswork.
In a world driven by data, these pillars are essential. They form the foundation of business analytics, guiding firms towards smarter, data-driven decisions. Understanding and applying these elements aids organizations in achieving their strategic goals. They optimize operations, improve customer experiences, and foster sustainable growth.
Business Analytics Solutions and Services: Unlocking Value for Enterprises
In today’s digital age, data is abundant but insights are scarce. Business analytics solutions bridge this gap. They transform raw data into actionable insights.
A strategic approach to analytics can unlock immense value. Solutions and services offer tailored insights for enhanced decision-making. Organizations derive key benefits from comprehensive analytics strategies. These include increased revenue, improved customer satisfaction, and optimized operations.
Effective business analytics services provide several offerings. These solutions help organizations harness data for competitive advantage. They include:
- Data Management: Collecting, cleansing, and organizing data efficiently
- Advanced Analytics: Employing sophisticated methods to analyze patterns
- Data Visualization: Presenting insights visually for easy understanding
- Predictive Modeling: Using historical data to forecast future events
Analytics services are scalable and flexible. They are designed to cater to various business sizes and industries. The uniqueness lies in customization, considering specific organizational needs and goals.
Consulting services guide businesses from strategy to execution. They develop tailored analytics roadmaps, aligning technology with business objectives. This ensures that solutions are not just technical but strategic.
Cost-efficiency is another critical advantage. By leveraging analytics, firms optimize resources and reduce waste. Data-driven decisions minimize risks, leading to more reliable outcomes.
Moreover, adopting these solutions fosters a culture of innovation. Teams are empowered with insights to drive creative solutions and improvements. This cultural shift positions businesses for future success.
In sum, business analytics solutions and services are indispensable in today’s data-driven marketplace. They go beyond simply managing data; they redefine how businesses operate and compete. With insightful analytics services, enterprises can unlock untapped value and achieve sustainable growth.
Key Benefits of Business Analytics for Mid-Sized Enterprises
Mid-sized enterprises often face unique challenges. They must navigate competitive landscapes with limited resources. Business analytics provides a strategic advantage, helping them thrive.
Firstly, analytics enhances efficiency. By optimizing business processes, enterprises can reduce costs and improve productivity. Streamlining operations allows for better resource allocation.
Secondly, it improves decision-making. With data-driven insights, leaders make informed decisions quickly. This agility is crucial in responding to market changes effectively.
Thirdly, analytics enhances customer understanding. Enterprises gain deeper insights into customer preferences and behaviors. This enables personalized services and improved customer satisfaction.
Key benefits include:
- Operational Efficiency: Streamlining processes to cut costs
- Informed Decision-Making: Quick access to actionable insights
- Customer Insight: Better understanding of customer needs
- Risk Mitigation: Proactive identification and management of risks
Moreover, risk management is more effective. Predictive analytics allows for anticipating potential risks. This proactive approach safeguards against unforeseen challenges.
Finally, analytics drives innovation. By uncovering trends and patterns, enterprises identify new opportunities. Innovation becomes a continuous cycle fueled by insights.
In essence, business analytics propels mid-sized enterprises toward success. It provides the tools needed to capitalize on opportunities and navigate challenges, ensuring sustainable growth.
Core Components: Data Collection, Cleaning, Analysis, and Visualization
Business analytics relies on several core components. Each step plays a vital role in transforming data into actionable insights. This process begins with data collection.
Data collection involves gathering relevant information from various sources. This may include internal databases, customer feedback, and market data. Accurate collection is essential for reliable analysis.
Once data is collected, the next step is data cleaning. This process ensures data accuracy and consistency. Cleaning involves removing duplicates, correcting errors, and filling in missing values. Clean data is the foundation for effective analytics.
Following cleaning is data analysis. Analysis involves examining the data to identify patterns and trends. Techniques include statistical analysis, machine learning, and predictive modeling. This step converts raw data into meaningful insights.
Key practices in data analysis:
- Statistical Techniques: Understanding patterns through numbers
- Machine Learning: Using algorithms for predictive insights
Data analysis leads to the final component: data visualization. Visualization transforms insights into easy-to-understand visual formats. Graphs, charts, and dashboards are common tools. This helps stakeholders grasp complex information quickly.
Visualization principles include:
- Clarity: Ensuring visuals are easy to interpret
- Relevance: Focusing on key insights
In summary, these core components form the backbone of business analytics. They work together to turn data into a powerful resource. By mastering these processes, enterprises can make informed and strategic decisions. This holistic approach drives innovation and competitive advantage.
Performance Analytics and Predictive Analytics: Driving Data-Driven Decisions
In today’s competitive landscape, data-driven decisions are crucial. Performance analytics and predictive analytics are key components in this decision-making framework. Each offers unique insights to guide businesses toward success.
Performance analytics focuses on evaluating past and current data. It identifies trends and assesses outcomes of past actions. By doing so, organizations can benchmark their successes and areas needing improvement. This type of analysis provides clarity on organizational achievements and pitfalls.
Predictive analytics, on the other hand, looks forward. It uses statistical techniques and machine learning models to foresee future events. This allows businesses to anticipate changes and prepare strategies accordingly. Predictive insights enable proactive rather than reactive decision-making.
Integrating these analytics types yields numerous benefits:
- Enhanced Planning: Better forecasting and budgeting
- Risk Mitigation: Identifying potential pitfalls before they occur
- Resource Optimization: Efficient allocation of resources
Together, performance and predictive analytics empower businesses with knowledge. This drives better decision-making and fosters a culture of continual improvement. In essence, they transform raw data into strategic assets, ensuring that organizations remain competitive and resilient in the face of change. Thus, embracing these analytics techniques is essential for any business seeking long-term success.
Business Intelligence and Data Analytics Services: From Insights to Action
Business intelligence (BI) and data analytics services provide the foundation for transforming raw data into actionable insights. These services offer a blend of tools and strategies to enhance decision-making. They help businesses navigate complexities and harness information effectively.
At the heart of BI services is data management. This involves collecting, storing, and organizing data efficiently. Businesses gain a structured view of their operations through effective data management systems. This foundation enables accurate and timely insights.
Next is the use of advanced analytics techniques. These techniques encompass data mining, pattern recognition, and statistical analysis. They uncover hidden trends and correlations within the data. This leads to deeper understanding and foresight for future planning.
The visualization of insights is another crucial aspect. User-friendly dashboards and reports facilitate data interpretation. These visual tools empower stakeholders to grasp complex information swiftly. As a result, informed decisions become accessible to all organizational levels.
Benefits of business intelligence and data analytics services include:
- Improved Reporting: Streamlined data reporting processes
- Operational Efficiency: Enhanced operational processes and workflows
- Strategic Growth: Informed strategic planning and market positioning
In conclusion, BI and data analytics services play a pivotal role in turning insights into actions. They ensure organizations stay agile and ahead in an ever-evolving marketplace. By leveraging these services, businesses can seamlessly bridge the gap from data collection to real-world application.
Analytics Consulting: Building a Data-Driven Culture
Analytics consulting is essential for cultivating a data-driven culture within organizations. It focuses on transforming how companies approach data and insights. Consultants guide businesses through adopting comprehensive data strategies.
A primary goal of analytics consulting is aligning data practices with business objectives. Consultants tailor solutions to fit the unique needs and goals of each enterprise. This alignment ensures that analytics initiatives truly support broader business aims.
Consultants also help optimize existing infrastructure. They assess current systems and recommend enhancements where needed. This might involve streamlining data collection processes or upgrading analytical tools for better performance.
Key benefits of engaging with analytics consulting include:
- Strategy Development: Crafting effective analytics strategies
- Skill Enhancement: Empowering teams through targeted training sessions
- Technology Integration: Guiding the implementation of cutting-edge tools
Ultimately, analytics consulting fosters a mindset shift across the organization. By embedding analytics into everyday operations, companies foster a culture where data guides every critical decision. This transformation promotes long-term adaptability and competitive advantage.
Leading Business Analytics Tools: Microsoft Fabric & Copilot, Tableau, Qlik, Alteryx, Databricks
In the realm of business analytics, choosing the right tools is crucial for success. Each enterprise has unique needs that dictate the choice of analytics solutions. Here, we explore several leading tools making waves in the industry.
Microsoft Fabric & Copilot provide seamless integration with business operations. They offer powerful data visualization and predictive analytics capabilities. These tools are ideal for enterprises seeking robust and scalable solutions.
Tableau is renowned for its intuitive data visualization features. It’s user-friendly, making it accessible to teams across an organization. Tableau transforms complex data sets into actionable insights.
Qlik stands out with its associative data indexing engine. It enables swift analysis and clear, interactive data visualizations. Qlik’s strength is its ability to uncover hidden insights quickly.
Alteryx excels in data preparation and blending. It offers an easy-to-use workflow for complex data processing tasks. Alteryx enhances the speed of analysis through automated processes.
Databricks is a cloud-based platform optimized for big data and machine learning. It facilitates collaboration between data scientists and engineers. Its strength lies in handling large-scale data transformations efficiently.
Each of these tools offers unique advantages:
- Integration & Scalability: Microsoft Fabric & Copilot
- Ease of Use & Visualization: Tableau
- Speed & Hidden Insights: Qlik
- Workflow Automation & Data Processing: Alteryx
- Big Data & Collaboration: Databricks
Selecting the right tool depends on specific business requirements. Consideration of company size, data complexity, and specific analytical goals is essential. Leveraging these tools can transform raw data into strategic business insights.
In conclusion, using advanced analytics tools enables better decision-making. They empower organizations to harness the full potential of their data. With the right tool in place, businesses can achieve competitive advantages and drive innovation.
Best Business Analytics Services Provider in India
When selecting a business analytics partner, Team Computers stands out in India. Their client-centric approach ensures tailored solutions that align with your strategic goals.
Team Computers excels in delivering end-to-end analytics services. Their expertise spans data integration, analysis, and visualization. With a focus on innovation, they transform data into actionable insights.
The company harnesses cutting-edge technologies, including Microsoft Fabric, Tableau, and Qlik. This technological prowess allows for seamless deployment and user-friendly experiences. Their solutions are designed to enhance decision-making and drive growth.
Team Computers values collaboration and long-term partnerships. They work closely with clients to understand unique challenges and objectives. This partnership model fosters trust and ensures mutual success.
Key advantages of choosing Team Computers include:
- Comprehensive Analytics Solutions: From data collection to visualization.
- Technological Expertise: Skilled in leading analytics tools.
- Tailored Approach: Custom solutions based on specific business needs.
- Collaborative Partnership: Client engagement and close collaboration.
- Proven Track Record: Successful analytics transformations across industries.
By choosing Team Computers, you’re investing in a partner dedicated to your success. They offer the expertise and tools needed to unlock the full potential of your data. Embrace analytics-driven growth with Team Computers as your guide.
How to Get Started: Steps to Implement Business Analytics in Your Organization
Embarking on the journey of business analytics requires a structured approach. Mid-sized enterprises should start with setting clear objectives. This helps in aligning analytics solutions with business goals.
Next, assess your current data infrastructure. Determine what tools and processes are already in place. This assessment will identify gaps and opportunities for improvement.
Once the assessment is complete, choose the right analytics tools and services. Consider options like Microsoft Fabric, Tableau, and Qlik. These tools offer robust features for comprehensive data analysis.
Finally, foster a culture of data-driven decision-making across your organization. Encourage teams to embrace insights and use them effectively.
Essential Steps to Implement Business Analytics:
- Define Objectives: Establish clear business goals.
- Assess Infrastructure: Evaluate current tools and data processes.
- Select Tools: Choose the right analytics platforms.
- Promote Data Culture: Encourage decisions based on data insights.
By following these steps, organizations can unlock the full potential of business analytics and drive sustainable growth.
Conclusion: The Future of Business Analytics
Business analytics will continue transforming decision-making landscapes. As technology evolves, the depth of insights will grow. For mid-sized enterprises, this presents a golden opportunity.
Adopting advanced analytics tools is essential for staying competitive. Team Computers stands out with innovative solutions tailored for various business needs. Their deep industry knowledge and technological prowess make them a preferred partner.
Choosing Team Computers means embracing a future-proof strategy. Clients benefit from cutting-edge tools like Microsoft Fabric, Tableau, and more. This partnership ensures not just growth, but sustainable success. Moving forward, leveraging business analytics effectively will be a critical differentiator in the marketplace.
The Team Computers Advantage
- Innovative, tailored solutions.
- Expertise in latest analytics tools.
- Focus on sustainable growth and success.